Setting password expiry for users in linux is essential. By setting up password expiration, you can ensure that users are reminded to update their passwords on a regular basis. In this guide, I will take you through the necessary steps to set up a default password expiration policy for new users in Linux.
Table of Contents
Global configuration in /etc/login.defs
The system-wide default settings for user accounts are stored in the /etc/login.defs file. To define the default password expiration policy, we’ll first modify this file.
Open the /etc/login.defs file in a text editor with root privileges:
#You can either use vim or nano text editor.
sudo vim /etc/login.defs
Set Password Expiry Values
Locate the following parameters in the login.defs file and adjust them according to your requirements
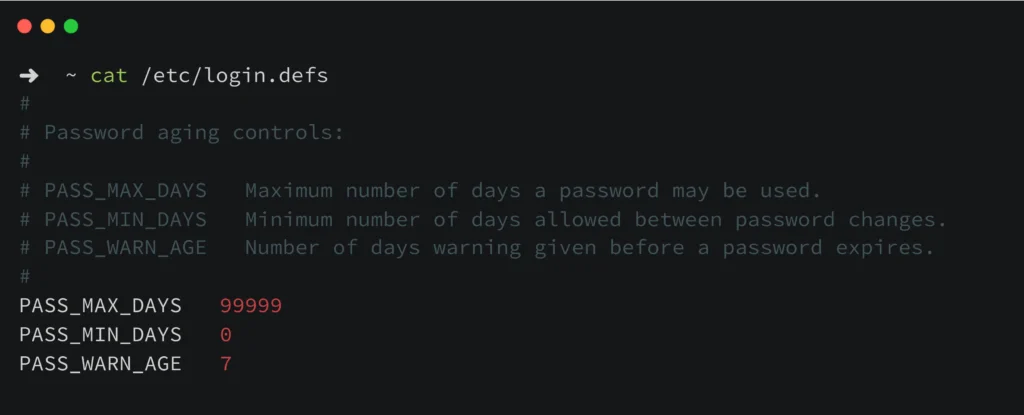
PASS_MAX_DAYS (Maximum Password Lifetime)
PASS_MAX_DAYS specifies you how many days a password can be used before it needs to be changed. It sets how long a user’s password is good for. The user will have to change their password after a certain number of days, like 90 days, in order to keep using their account. Setting a maximum password lifetime helps make sure that passwords are changed regularly, which lowers the risk of someone getting in without permission after a password has been stolen.
If PASS_MAX_DAYS is set to 90, users will need to change their passwords every 90 days.
PASS_MAX_DAYS 90
PASS_MIN_DAYS (Minimum Password Change Interval)
The PASS_MIN_DAYS setting tells how many days must pass before a person can change their password again. It sets a countdown timer after you change your password. Users can’t change their passwords again until this certain amount of time has passed. It stops people from changing passwords frequently or from using old passwords frequently.
If PASS_MIN_DAYS is set to 7, users must wait at least 7 days before they can change their password again.
PASS_MIN_DAYS 7
PASS_WARN_AGE (Password Expiry Warning Period)
PASS_WARN_AGE specifies the number of days before password expiration that users start receiving warnings. It controls when users receive notifications about their expiring passwords. It alerts users in advance so they can prepare to change their passwords before they expire. It forces responsible password management and reduces the users being locked out due to expired passwords.
If PASS_WARN_AGE is set to 7, users will start receiving warnings 7 days before their password expires.
PASS_WARN_AGE 7
Modify these parameters according to your need. Save and close the file once you’ve made the changes.
Verify Changes
To ensure that the changes take effect for new users, verify that these settings are correctly applied.
Create New Users
From now on, any new user accounts created on the system will inherit these default password expiration settings. When a new user is added, their password will automatically expire based on the parameters defined in /etc/login.defs.
Set Password Expiry for Existing Users
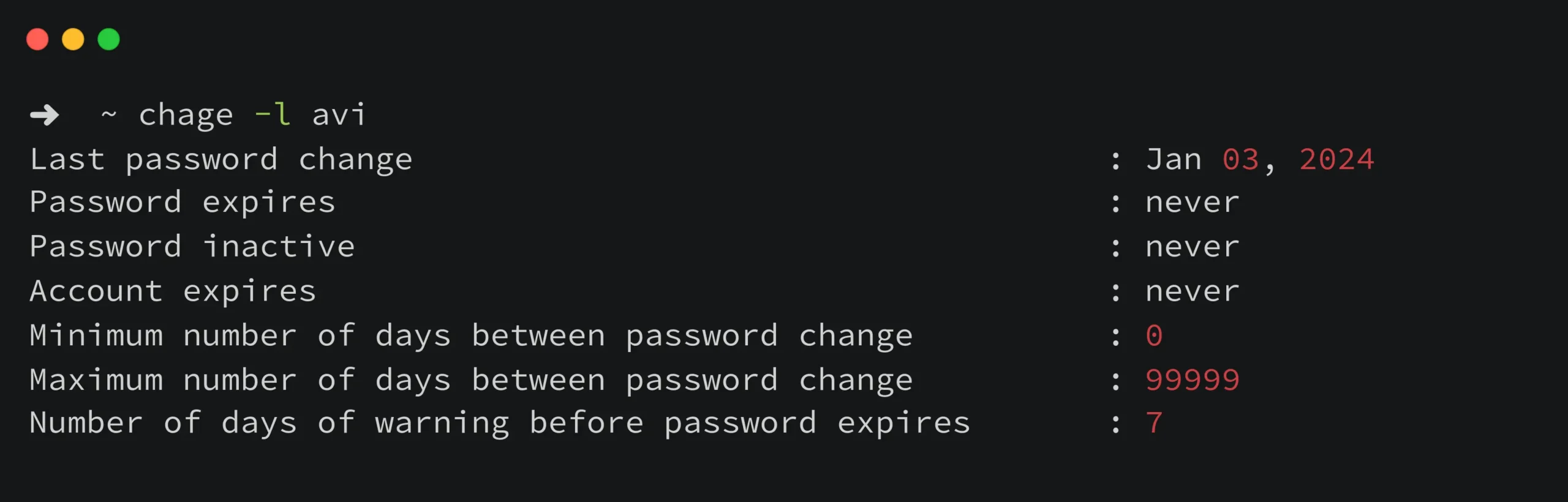
To apply these settings to existing users, you can use the chage command.
Checking the password aging settings.
sudo chage -l <username>
To force a user to change their password upon next login
sudo chage -d 0 <username>
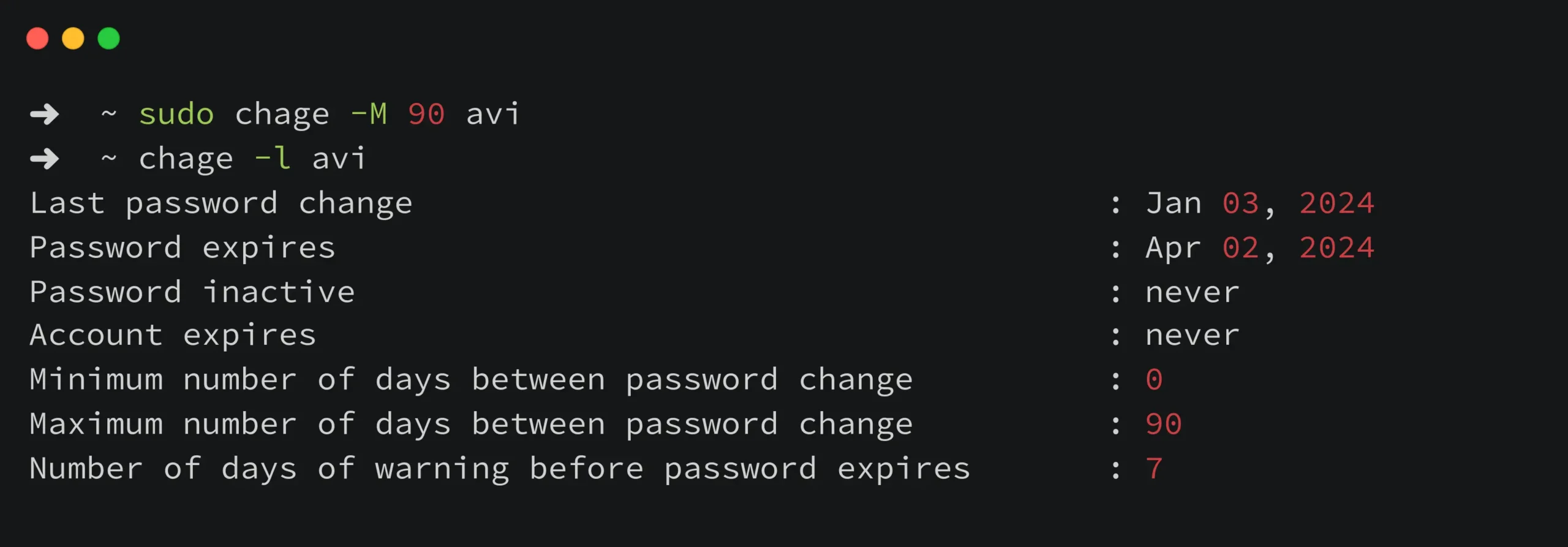
Set the Maximum Number of Days for Password Expiry Using Chage
To set the maximum number of days before the password expires for a user, use the --maxdays (-M) option with the chage command.
sudo chage --maxdays <number_of_days> <username>
This command will configure the system to expire the user’s password after 90 days. The user will be prompted to change their password upon expiration according to this policy.
Disable Password Expiration
Use the chage command with the --maxdays (-M) option to set a high value:
sudo chage --maxdays 99999 <username>
Replace <username> with the username of the user you want to modify.
Password Policies
Consider implementing additional password policies such as complexity requirements such as minimum length, character types using tools like pam_pwquality.so (Pluggable Authentication Modules) for more robust security.
By configuring default password expiry settings, you enhance the security posture of your Linux system by ensuring that passwords are regularly updated. This reduces the risk of unauthorized access due to compromised credentials. It helps you system in fundamental step towards improving overall system security.
chage Command Manual: chage(1) — Linux manual page
See also: Other posts tagged in How To
Got any queries or feedback? Feel free to drop a comment below!


One of the best articles I’ve read on the topic—clear,
concise, and very useful.